Wisdom - Windows
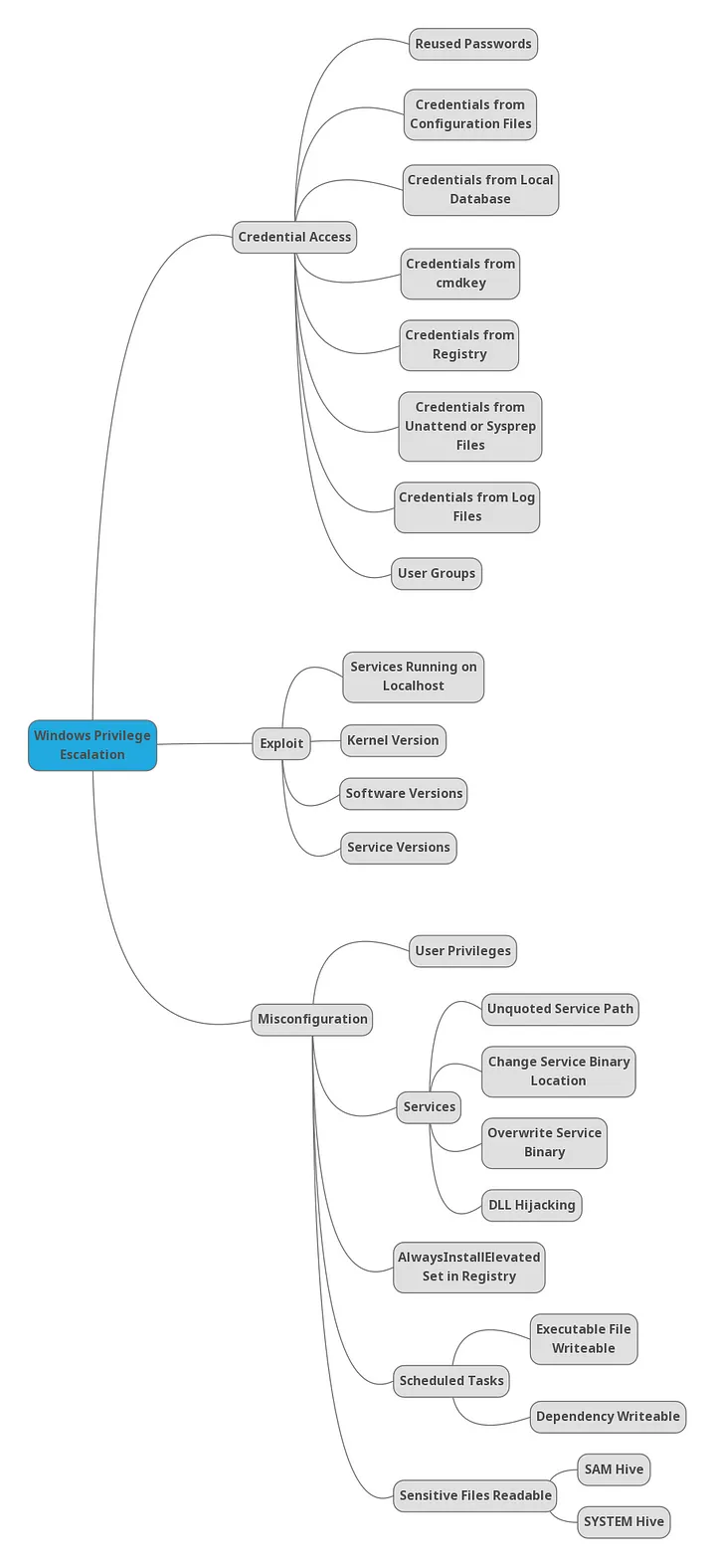
Enumeration is key to everything
- Hidden credentials
- Vulnerabilities with an existing exploit
- Misconfigured software
- Nested vulnerabilities
Some of the AD boxes aren't actually AD exploits, they just happen to be running AD. Some people reporting:
- Initial privesc not AD related
- AD account was useless in pivoting (could have been a local account and the outcome would've been the same)
- Next privesc was not AD related
Be considerate of this with AD boxes. Basically it's entirely possible to hack AD boxes without AD sometimes.
Bloodhound, bloodhound, bloodhound for the AD set
Carefully enumerate Console_Host (PowerShell history)
Check the files of all users as well as root of C:\ for scripts, installers, backups or creds
Run WinPEAS after EVERY privesc, Mimikatz on Domain Admin or SeImpersonate Priv
Are tools like PuTTY or RDCMan installed?